Ausgefeilte Cyberbedrohungen können herkömmliche Sicherheitswerkzeuge umgehen, indem sie sich schneller verändern, als sich signaturbasierte Erkennungsmechanismen und Reputationsdaten anpassen können. Angreifer modifizieren regelmäßig Malware-Varianten, ändern Indikatoren für böswilliges Verhalten und verbergen schädliche Aktivitäten in scheinbar legitimen Dateien.
Um diese Bedrohungen zu erkennen, benötigen Sicherheitsteams Informationen, die verschiedene Indikatoren miteinander verknüpfen, wie beispielsweise Reputationsindikatoren, Verhaltensmerkmale und Zusammenhänge zwischen Malware-Varianten.
Die Threat Intelligence hinter MetaDefender bewältigt diese Herausforderung durch die Verknüpfung von Reputationsdaten, in Sandboxen generierten IOCs (Indikatoren für Kompromittierung) und der auf maschinellem Lernen basierenden Suche nach Ähnlichkeiten bei Bedrohungen. Dies hilft Sicherheitsteams dabei, Zero-Day-Bedrohungen aufzudecken und Zusammenhänge zwischen bekannten bösartigen Mustern und Aktivitäten zu erkennen.
Bei der Bereitstellung über MetaDefender for Core wird diese Intelligence direkt in lokalen und luftisolierten Umgebungen eingesetzt. Unternehmen können verdächtige Dateien mithilfe einer emulationsbasierten dynamischen Analyse untersuchen und die Ergebnisse durch korrelierte Bedrohungsinformationen ergänzen, um schwer zu erkennende und bisher unbekannte Bedrohungen zu identifizieren.
Warum Threat Intelligence , die sich ausschließlich auf Reputation stützt, zu kurz Threat Intelligence
Herkömmliche Plattformen für Bedrohungsinformationen stützen sich auf Reputationsindikatoren wie Datei-Hashes, IP-Adressen, Domains und URLs. Diese Indikatoren können zwar dabei helfen, bekannte Bedrohungen zu identifizieren, liefern jedoch nur begrenzte Informationen, wenn Angreifer Malware modifizieren oder bösartige Indikatoren wie Domains oder IP-Adressen ändern.
Einschränkungen der reputationsbasierten Threat Intelligence
| Grenzen der reputationsbasierten Intelligenz | Auswirkungen auf die Sicherheitsteams |
|---|---|
| Hash-basierte Indikatoren lassen sich leicht ändern | Schädliche Dateien können die Reputationserkennung umgehen, wenn sich die Indikatoren ändern |
| Den Indikatoren fehlt der Verhaltenskonttext | Analysten können nicht nachvollziehen, wie sich eine Datei während der Ausführung verhält |
| Indikatoren treten isoliert auf | Es ist schwer festzustellen, ob damit verbundene böswillige Aktivitäten vorliegen |
| Die Informationen aus nachrichtendienstlichen Quellen sind lückenhaft | Analysten müssen zwischen verschiedenen Tools wechseln, um Bedrohungen zu untersuchen |
Die Threat Intelligence überwindet diese Einschränkung durch die Verknüpfung verschiedener Arten von Informationen. Anstatt sich ausschließlich auf statische Indikatoren zu stützen, kombiniert die Engine Reputationsdaten mit Verhaltensmerkmalen, die aus dynamischen Analysen gewonnen wurden, sowie mit Ergebnissen der Ähnlichkeitssuche zwischen verwandten Proben.
Dieser Ansatz ermöglicht es Sicherheitsteams, über einzelne Indikatoren hinauszugehen und Muster zu erkennen, die bisher unbekannte Malware-Varianten identifizieren, indem sie diese mit bekannten bösartigen Mustern in Zusammenhang bringen.
Wie die Threat Intelligence Indikatoren miteinander verknüpft
Durch die Analyse sowohl statischer Indikatoren als auch verhaltensbasierter Merkmale kann das System Zusammenhänge zwischen schädlichen Dateien, zugehörigen Indikatoren und bekannten schädlichen Aktivitäten aufdecken. Die Threat Intelligence ist Teil einer vierstufigen Zero-Day-Erkennungs-Pipeline, die in die Umgebung gelangende Dateien analysiert. Jede Stufe liefert eine andere Art von Informationen, die das Gesamturteil untermauern.
1. Bedrohungsbewertung
In der ersten Phase werden Dateien und zugehörige IOCs anhand globaler Indikatoren aus dem Bereich der Bedrohungserkennung überprüft. Dateien, URLs, Domains und IP-Adressen werden mit bekannten Indikatoren für bösartige Aktivitäten abgeglichen, um bereits bekannte Bedrohungen schnell zu identifizieren.
2. Dynamische Analyse
Wenn Dateien nicht allein durch Reputationsprüfungen klassifiziert werden können, werden sie in einer auf Emulation basierenden Umgebung für dynamische Analysen ausgeführt. In dieser Phase entstehen Verhaltensmerkmale wie abgelegte Dateien, Änderungen an der Registrierungsdatenbank, Ausführungsketten und Netzwerk-Callbacks, die Aufschluss darüber geben, wie sich die Datei während der Ausführung verhält.
3. Bedrohungsbewertung
Aus der dynamischen Analyse gewonnene Verhaltensmerkmale werden mit Reputationsindikatoren abgeglichen, um verdächtige Aktivitäten zu bewerten.
4. Suche nach ähnlichen Bedrohungen
In der letzten Phase wird eine auf maschinellem Lernen basierende Suche nach Ähnlichkeiten bei Bedrohungen durchgeführt, um strukturelle und verhaltensbezogene Ähnlichkeiten zwischen den Proben zu erkennen. Auf diese Weise kann die Engine bisher unbekannte Dateien identifizieren, indem sie diese mit bekannten Schadmustern abgleicht.
Zusammen verwandeln diese Analysefunktionen einzelne Indikatoren in miteinander verknüpfte Bedrohungsinformationen. Sicherheitsteams erhalten einen tieferen Einblick darin, wie sich Dateien verhalten, in welchem Zusammenhang sie mit bekannten Angriffen stehen und ob sie eine neue Variante einer bestehenden Bedrohung darstellen.

Threat Intelligence für MetaDefender Core
Bei der Bereitstellung über MetaDefender for Core arbeitet die Threat Intelligence direkt innerhalb der lokalen Sicherheitsumgebungen. Dadurch können Unternehmen verdächtige Dateien analysieren, ohne Daten an externe Dienste zu übermitteln, was für regulierte oder isolierte Umgebungen von entscheidender Bedeutung ist.
Die Engine arbeitet mit den auf Emulation basierenden Funktionen zur dynamischen Analyse von MetaDefender zusammen. Dateien, die in die Umgebung gelangen, werden in einer kontrollierten Analyseumgebung ausgeführt, in der das System das Verhalten der Dateien beobachtet und IOCs extrahiert.
Diese Verhaltensmerkmale werden anschließend von der Threat Intelligence miteinander in Beziehung gesetzt. Reputationsindikatoren liefern Kontextinformationen zu bekannten Schadindikatoren, während in der Sandbox generierte Indikatoren Aufschluss darüber geben, wie sich die Datei während der Ausführung verhält. Bei der Suche nach Ähnlichkeiten zwischen Bedrohungen werden die Verhaltens- und Strukturmerkmale von Dateien mit zuvor analysierten Proben verglichen.
Von der Threat Intelligence verwendete Informationsquellen
| Nachrichtendienstliches Signal | Quelle | Was sich daraus ergibt |
|---|---|---|
| Reputationsindikatoren | Engine zur Bewertung der Bedrohungsreputation | Bekannte Indikatoren für bösartige Software |
| Verhaltensartefakte | Dynamische Analyse | Wie sich die Datei während der Ausführung verhält |
| Strukturelle Merkmale | Dateiprüfung | Verdächtige Dateistruktur oder Komprimierung |
| Suche nach ähnlichen Bedrohungen | Datei: Ähnlichkeitsanalyse mittels maschinellem Lernen | Strukturelle und verhaltensbezogene Ähnlichkeiten zwischen den analysierten Dateien |
Da der Motor in derselben Umgebung wieCore MetaDefender Core läuft, können Unternehmen diese Analyse direkt in bestehende Pipelines zur Dateiverarbeitung integrieren. Verdächtige Dateien, die über E-Mail-Gateways, Dateiübertragungsplattformen, Speicherscans oder andere Kontrollpunkte übermittelt werden, können analysiert und mit Bedrohungsinformationen abgeglichen werden, bevor sie interne Systeme erreichen.
Diese Architektur integriert Verhaltensanalysen und Bedrohungsinformationen direkt inCore MetaDefender Core . Dadurch können Unternehmen schwer zu erkennende Bedrohungen identifizieren und gleichzeitig die volle Kontrolle über sensible Daten behalten.
Sicherheitsherausforderungen und wie die Threat Intelligence diese bewältigt
Sicherheitsteams nutzen häufig separate Tools, um Bedrohungen zu erkennen, das Verhalten von Malware zu analysieren und damit verbundene Angriffe zu untersuchen. Diese Fragmentierung verlangsamt die Untersuchungen und erschwert es, Indikatoren über verschiedene Phasen eines Angriffs hinweg miteinander in Verbindung zu bringen.
Die Threat Intelligence bewältigt diese Herausforderungen, indem sie Reputationsindikatoren, Verhaltensmerkmale und zugehörige Samples innerhalb einer einheitlichen Intelligence-Pipeline miteinander verknüpft.
Begrenzte Kontextinformationen aus Reputationsdaten
Wenn Angreifer Malware-Varianten modifizieren, reichen Reputationsindikatoren allein möglicherweise nicht aus, um die tatsächliche Bedrohung aufzudecken. Durch die Verknüpfung von Verhaltensmerkmalen, die bei der dynamischen Analyse extrahiert wurden, mit Reputationsindikatoren und der Suche nach Ähnlichkeiten bei Bedrohungen liefert die Threat Intelligence einen tieferen Kontext für die Bewertung verdächtiger Dateien und die Identifizierung bisher unbekannter Malware-Varianten.
Untersuchungssilos
In vielen Umgebungen werden Sandbox-Analysen, Reputationsabfragen und die Suche nach Ähnlichkeiten bei Bedrohungen in separaten Tools durchgeführt. Analysten müssen zwischen den Systemen hin- und herwechseln, um festzustellen, ob eine verdächtige Datei Teil eines größeren Angriffs ist.
Die Threat Intelligence korreliert diese IOCs automatisch, sodass Analysten Verhaltensmuster, zugehörige Indikatoren und analysierte Dateien im Rahmen eines einzigen Untersuchungsprozesses einsehen können. Dies verkürzt die Untersuchungsdauer und hilft den Analysten dabei, festzustellen, ob eine Datei mit bekannten böswilligen Aktivitäten in Verbindung steht oder eine neue Bedrohung darstellt.
Transparenz in eingeschränkten oder isolierten Umgebungen
Viele Unternehmen, die kritische Infrastrukturen betreiben, können sich nicht auf cloudbasierte Bedrohungsanalysen verlassen. Mit MetaDefender for Core die Threat Intelligence direkt in lokalen Umgebungen eingesetzt werden, sodass verdächtige Dateien auch ohne Verbindung zum Internet analysiert werden können.
Zuverlässige Indikatoren für eine Kompromittierung
Die dynamische Analyse generiert Verhaltensartefakte wie abgelegte Dateien, Netzwerk-Callbacks, Registrierungsänderungen und Ausführungsketten. In Verbindung mit Reputationsindikatoren und der Suche nach Ähnlichkeiten bei Bedrohungen liefern diese Artefakte hochpräzise IOCs, die eine schnellere Untersuchung und Reaktion ermöglichen.
Wo die Threat Intelligence inCore von MetaDefender eingebunden ist
In vielen Unternehmen gelangen verdächtige Dateien über verschiedene Kanäle wie E-Mail-Anhänge, Dateiübertragungen, Uploads und Wechseldatenträger in die Systemumgebung. Sicherheitsteams benötigen eine Möglichkeit, diese Dateien zu analysieren, ohne den normalen Geschäftsablauf zu stören oder sensible Daten gegenüber externen Systemen offenzulegen.
Bei der Bereitstellung über MetaDefender for Core wird die Threat Intelligence Teil der Dateiüberprüfungspipeline innerhalb von MetaDefender Core. Verdächtige Dateien können analysiert werden, während sie die bestehenden Sicherheitskontrollen durchlaufen, sodass Unternehmen Bedrohungen erkennen können, bevor die Dateien interne Systeme erreichen.
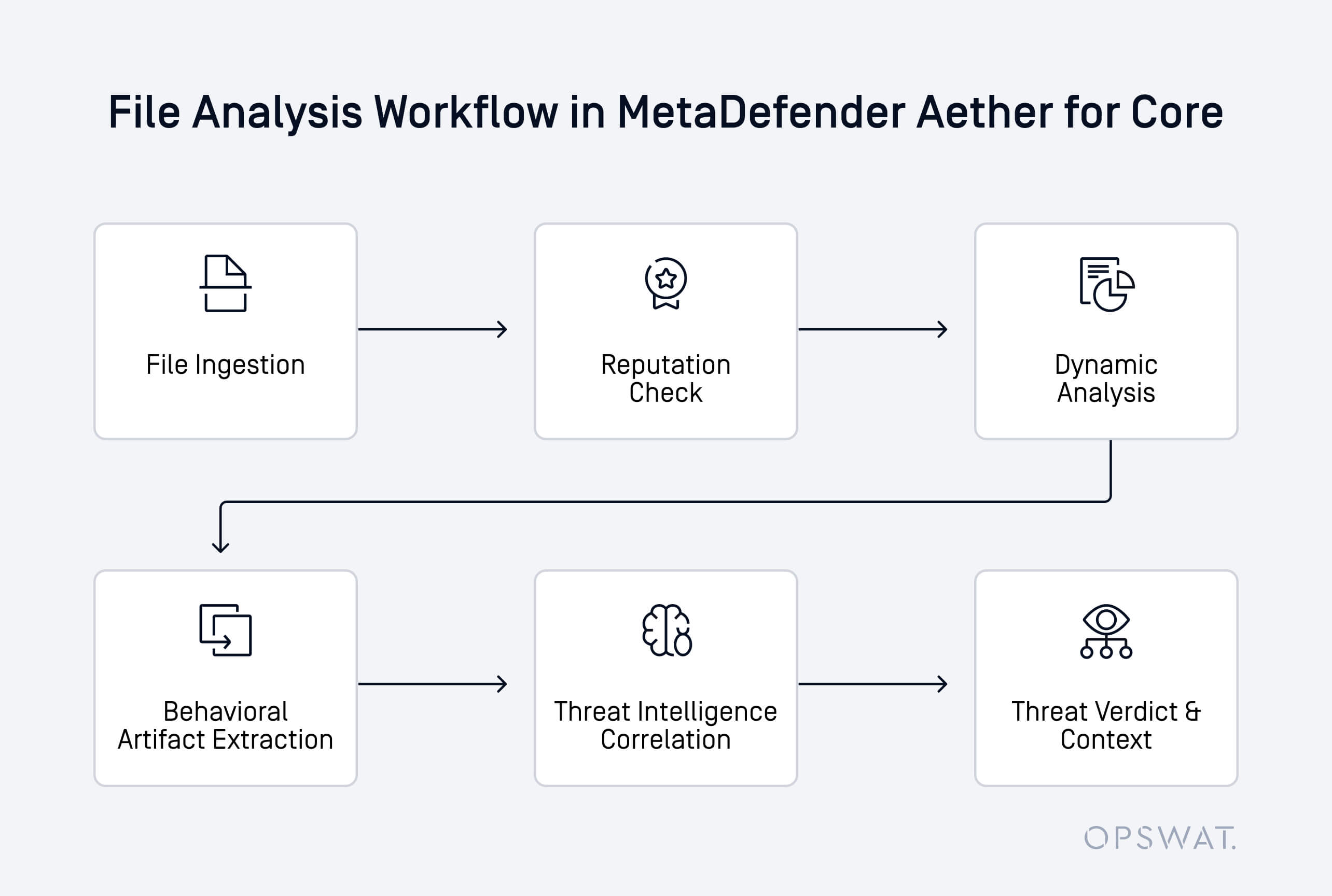
InnerhalbCore folgt der Analyseprozess in der Regel einem strukturierten Ablauf:
- Eine Datei gelangt über eine Content-Pipeline – beispielsweise per E-Mail, Upload oder Dateiübertragung – in die Umgebung
- Bei der statischen Überprüfung und der Reputationsprüfung wird geprüft, ob die Datei bekannten Bedrohungen entspricht
- Verdächtige oder unbekannte Dateien werden in einer auf Emulation basierenden Umgebung zur dynamischen Analyse ausgeführt
- Verhaltensartefakte wie abgelegte Dateien, Änderungen an der Registrierungsdatenbank, Ausführungsketten und Netzwerk-Callbacks werden extrahiert
- Die Threat Intelligence gleicht diese Artefakte mit Reputationsdaten ab und führt eine Suche nach Ähnlichkeiten bei Bedrohungen durch
- Das System liefert ein endgültiges Ergebnis mit kontextbezogener Intelligenz, die Analysten dabei hilft, das Risiko einzuschätzen
Da der Motor direkt innerhalb der MetaDefender Core läuft, können Unternehmen diese Informationen an mehreren Kontrollpunkten nutzen. Dateien, die über E-Mail-Gateways, Dateiübertragungssysteme, Speicherplattformen und andere Content-Workflows eingehen, können alle von derselben korrelierten Analyse profitieren.
Dank dieser Integration können Sicherheitsteams verhaltensbasierte Bedrohungsinformationen direkt in ihre operativen Arbeitsabläufe einbinden. So können sie verdächtige Dateien früher erkennen und gleichzeitig eine einheitliche Überprüfung in der gesamten Umgebung gewährleisten.
Warum verhaltensbasierte Threat Intelligence für die Erkennung von Zero-Day-Angriffen entscheidend Threat Intelligence
Malware stützt sich selten auf einen einzigen statischen Indikator. Daher benötigen Sicherheitsteams Informationen, die sich eher auf das Verhalten und die Zusammenhänge zwischen Angriffen konzentrieren als auf isolierte Indikatoren.
Verhaltensorientierte Bedrohungsinformationen bewältigen diese Herausforderung, indem sie verschiedene Indikatoren miteinander verknüpfen, die Aufschluss über das Verhalten bösartiger Dateien geben. Anstatt sich ausschließlich auf Reputationsdaten zu stützen, analysiert die Threat Intelligence das Ausführungsverhalten, zugehörige IOCs und Gemeinsamkeiten zwischen den analysierten Dateien, um zu beurteilen, ob diese verdächtig sind.
Dieser Ansatz verbessert die Erkennung durch:
- Erkennung bisher unbekannter Bedrohungen durch die Analyse von Verhaltensmustern
- Aufdeckung von Zusammenhängen zwischen Malware-Varianten, die ähnliche Ausführungsmuster aufweisen
- Verdächtige Dateien mit entsprechenden böswilligen Aktivitäten und zugehörigen IOCs in Verbindung bringen
- Bereitstellung kontextbezogener Informationen, die Analysten dabei helfen, die Absicht einer Datei zu verstehen
In MetaDefender for Core werden diese Funktionen zusammen mit einer emulationsbasierten dynamischen Analyse eingesetzt. Die Sandbox-Umgebung deckt verstecktes Verhalten auf, während die Threat Intelligence die dabei gewonnenen Artefakte mit Reputationsindikatoren und zuvor analysierten Proben abgleicht.
Durch die Kombination dieser Verhaltensmerkmale können Unternehmen Zero-Day-Malware erkennen, die andernfalls der signaturbasierten Erkennung oder Reputations-Feeds entgehen würde. So können Sicherheitsteams bisher unbekannte Bedrohungen früher identifizieren und reagieren, bevor sich Angriffe in der Umgebung ausbreiten.
Unbekannte Bedrohungen schneller erkennen – dank verhaltensbasierter Threat Intelligence
Bei der Bereitstellung über MetaDefender for Core läuft die Threat Intelligence direkt in der Umgebung des Unternehmens. Sicherheitsteams können verdächtige Dateien mithilfe einer emulationsbasierten dynamischen Analyse untersuchen und die Ergebnisse mit Bedrohungsdaten abgleichen, um bisher unbekannte Dateien und damit verbundene böswillige Aktivitäten aufzudecken.
Durch die direkte Integration der Korrelation von Bedrohungsinformationen inCore MetaDefender Core können Unternehmen Dateien bereits in einer früheren Phase des Prüfprozesses analysieren und erhalten einen besseren Überblick über verdächtige Aktivitäten, bevor Bedrohungen interne Systeme erreichen.
Stärken Sie Ihre Strategie zur Erkennung von Zero-Day-Angriffen mit verhaltensbasierten Bedrohungsinformationen. Sprechen Sie mit unseren Experten, um zu erfahren, wie die Threat Intelligence die Erkennung in IhrenCore verbessern kann.

