Mit der Verabschiedung der Verordnung (EU) 2024/2847, auch bekannt als CRA (Cyber Resilience Act), hat die Europäische Union ihre Cybersicherheitsstandards deutlich angehoben. Als erste horizontale Cybersicherheitsverordnung für PDEs (Produkte mit digitalen Elementen) legt der CRA rechtsverbindliche Sicherheitsanforderungen sowohl für Hardware als auch für Software fest, die auf den EU-Markt gebracht werden.
Im Jahr 2024 wurden durch die Verordnung verbindliche Cybersicherheitsverpflichtungen für den gesamten Produktlebenszyklus formell eingeführt, von der sicheren Entwicklung über die Sorgfaltspflicht bei Komponenten von Drittanbietern bis hin zum Umgang mit Sicherheitslücken und der Meldung von Vorfällen.
Ab September 2026 sind Hersteller verpflichtet, aktiv ausgenutzte Sicherheitslücken und schwerwiegende Sicherheitsvorfälle zu melden. Bis Dezember 2027 muss die vollständige Einhaltung der Vorschriften gewährleistet sein, einschließlich der Dokumentation, der Sicherheitskontrollen während des gesamten Lebenszyklus undBill of Materials (SBOM) .
Für CIOs, CISOs, Verantwortliche für Produktsicherheit und Compliance-Teams hat die CRA operative, finanzielle und regulatorische Konsequenzen. Unternehmen müssen in der Lage sein, „Secure-by-Design“-Praktiken nachzuweisen, eine kontinuierliche Schwachstellenüberwachung einzuführen, eine auditfähige SBOM-Dokumentation zu führen und die Transparenz der Lieferkette sowohl bei proprietären als auch bei Open-Source-Komponenten sicherzustellen.
Dieser Artikel bietet einen praktischen Leitfaden zur Einhaltung der CRA-Vorschriften und behandelt dabei die Verpflichtungen in der Software-Lieferkette, die Anforderungen an die SBOM, die Verantwortlichkeiten während des Lebenszyklus sowie strategische Maßnahmen, die Unternehmen jetzt ergreifen sollten, um sich auf die Durchsetzung der Vorschriften vorzubereiten.
Überblick über die Anforderungen des Gesetzes zur Cyber-Resilienz
Was ist das Gesetz zur Cyber-Resilienz und warum wurde es eingeführt?
Die CRA schafft den ersten EU-weiten horizontalen Rahmen für die Cybersicherheit von Produkten mit digitalen Elementen.
Die Verordnung zielt darauf ab:
- Systemische Schwachstellen bei vernetzten Produkten reduzieren
- Die Transparenz in Software-Lieferketten verbessern
- Sicherstellung des Schwachstellenmanagements über den gesamten Lebenszyklus hinweg
- Die Verantwortung auf die Hersteller verlagern
Wer muss die Vorschriften einhalten?
- Software
- Hardware , die Software integrieren
- Importeure und Händler
- Entwickler, die Komponenten von Drittanbietern oder Open-Source-Komponenten integrieren
- Anbieter kritischer oder wichtiger digitaler Produkte
Supply Chain Software Supply Chain gemäß dem CRA
Sorgfaltsprüfung bei Komponenten
Hersteller müssen bei Komponenten von Drittanbietern eine Sorgfaltsprüfung durchführen, einschließlich der Bewertung bekannter Schwachstellen und der Überwachung von Sicherheitsupdates.
Durchgängige Verantwortung für Sicherheitslücken
Die Hersteller bleiben für Sicherheitslücken in allen integrierten Komponenten verantwortlich, unabhängig von deren Herkunft.
Secure und Secure
Produkte müssen mit sicheren Standardkonfigurationen ausgeliefert und von Anfang an unter Berücksichtigung der Cybersicherheit entwickelt werden.
Überwachung und Meldung von Sicherheitslücken
Aktiv ausgenutzte Sicherheitslücken und schwerwiegende Vorfälle müssen ab September 2026 gemeldet werden.
Technische Dokumentation und Aufbewahrung
Sicherheitsunterlagen, einschließlich SBOMs (Software of Materials), müssen nach dem Inverkehrbringen des Produkts zehn Jahre lang aufbewahrt werden.
SBOM-Anforderungen gemäß dem CRA
Die CRA verpflichtet Hersteller dazu, die in Produkten mit digitalen Elementen verwendeten Softwarekomponenten zu dokumentieren, in der Regel mithilfe von SBOMs, die als Teil der technischen Dokumentation des Produkts geführt werden. Zwar schreibt die Verordnung keine bestimmten SBOM-Felder vor, doch enthalten branchenübliche SBOMs in der Regel Komponentenkennungen, Versionsinformationen, Angaben zu Lieferanten oder Herkunft, Abhängigkeitsbeziehungen sowie Integritätsdaten wie kryptografische Hashes.
Die SBOM muss folgende Anforderungen erfüllen:
- Maschinenlesbar
- Wird als Teil der technischen Dokumentation gepflegt
- wird den EU-Behörden auf begründeten Antrag hin zur Verfügung gestellt
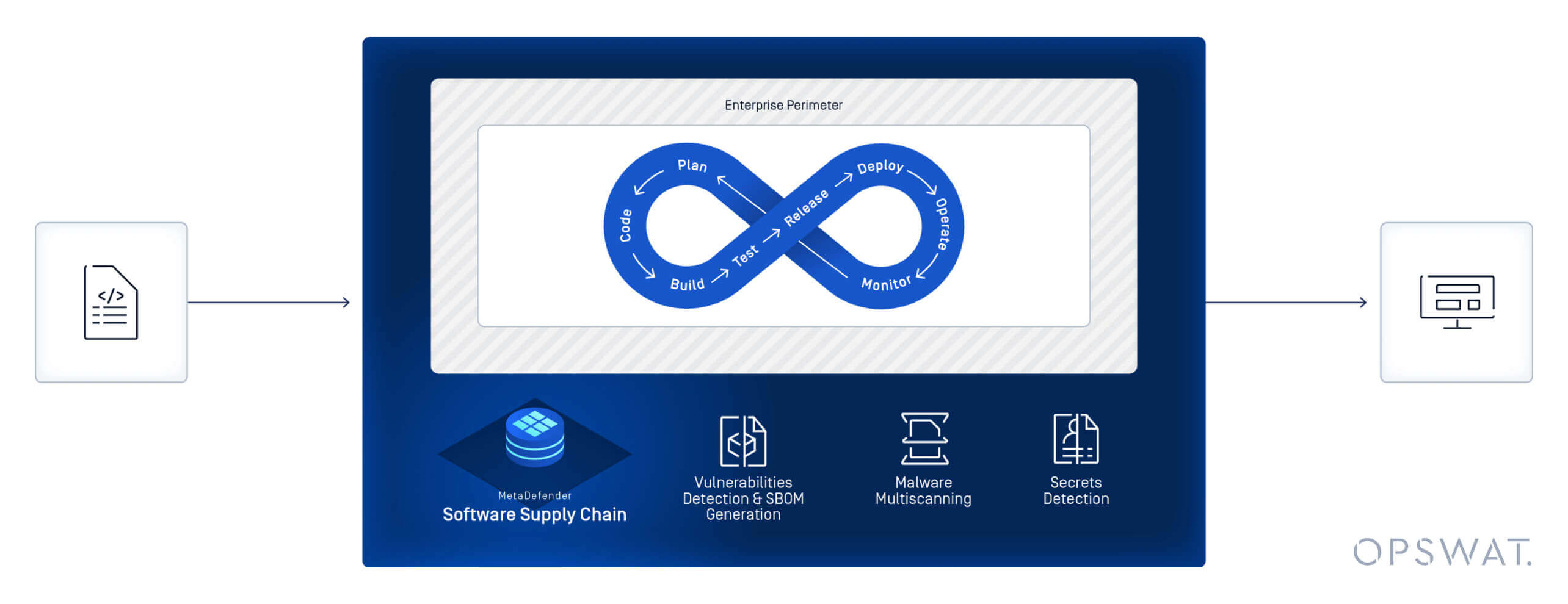
Wie OPSWAT Supply Chain Software Supply Chain im Rahmen des CRA OPSWAT
1. Transparenz bei Software
- Bezeichnung, Version und Lieferantenangaben der Komponente
- Abbildung direkter und transitiver Abhängigkeiten
- Eindeutige Kennungen und kryptografische Validierung
- Zentralisierte SBOM-Verwaltung
2. Transparenz und Risikoerkennung
- Vulnerability detection öffentlicher Datenbanken
- Malware-Prüfung in Softwarepaketen
- Erkennung versteckter Risiken vor der Freigabe
- Kontinuierliche Überwachung auf neue CVEs
3. Dokumentation und Prüfungsbereitschaft
- Erstellung maschinenlesbarer SBOMs (CycloneDX, SPDX)
- Exportierbare Berichte
- Secure und kontrollierte Freigabe
Anpassung von Software an die CRA-Vorschriften
| Komponententyp | Beispiel | Erforderliche Sichtbarkeit | Verantwortung |
|---|---|---|---|
| Hauptanwendung | SaaS-Plattform für Unternehmen | Vollständige SBOM auf Produktebene | Hersteller |
| Core | OpenSSL | Überwachung auf oberster Ebene und Schwachstellenüberwachung | Hersteller |
| Middleware/Laufzeitumgebung | Webserver oder Container-Laufzeitumgebung | Überprüfung der Abhängigkeiten | Hersteller + Anbieter |
| Bibliotheken von Drittanbietern | SDKs, APIs | Transitive Einbeziehung in die SBOM | Hersteller |
Ein praktischer Leitfaden zur Einhaltung der CRA-Vorschriften
1. Eine Bereitschaftsprüfung durchführen
Bewerten:
- Aktuelle Verfahren zur Software-Bestandsaufnahme
- Erstellung bestehender SBOMs
- Reifegrad der Schwachstellenüberwachung
- Verfahren zur Aufbewahrung von Unterlagen
2. Interne Governance etablieren
Legen Sie klare Rollen fest für:
- Entwickler
- DevOps-Teams
- Sicherheitsteams
- Recht/Compliance
- Beschaffung
3. Automatisierung der SBOM-Erstellung
Tools sollten:
- Erstellen Sie für jede Version und jedes Update eine SBOM
- In CI/CD-Pipelines integrieren
- Ausgabe in den Formaten CycloneDX und SPDX
- Erforderliche Mindestangaben überprüfen
4. SBOM in den gesamten Softwareentwicklungszyklus integrieren
Die Reife der SBOM entwickelt sich in verschiedenen Phasen:
- Entwurf der SBOM (geplante Komponenten)
- SBOM erstellen (kompilierte Artefakte)
- Analysierte SBOM (Prüfung nach der Erstellung)
- Bereitgestellte SBOM (Produktionsumgebung)
- Laufzeit-SBOM (aktive Überwachung)
5. Kontinuierliche Einhaltung der Vorschriften und Überwachung sicherstellen
- Schwachstellendatenbanken kontinuierlich überwachen
- SBOMs aktualisieren, wenn sich Komponenten ändern
- Workflows für die Offenlegung von Sicherheitslücken einrichten
- Unterlagen für behördliche Anfragen vorbereiten
Gemäß dem CRA akzeptierte SBOM-Formate
CycloneDX
Sicherheitsorientiert, optimiert für das Schwachstellenmanagement.
SPDX
Auf Lizenzen ausgerichtet, weit verbreitet für die Dokumentation der Compliance.
So bewerten Sie CRA-konforme Compliance-Lösungen
Berücksichtigen Sie bei der Auswahl von Anbietern oder Tools Folgendes:
- Erstellung von SBOMs in gängigen Formaten
- Integration mit DevOps und Container-Registries
- Kontinuierliche Überwachung von Sicherheitslücken
- Funktionen zur Malware-Prüfung
- Prüfungsgerechte Berichterstattung
- Secure Datenspeicherung und -freigabe
Fragen Sie die Anbieter:
- Wie oft werden SBOMs aktualisiert?
- Wie gehst du mit transitiven Abhängigkeiten um?
- Wie wird die Schwachstellenanalyse integriert?
- Wie unterstützen Sie die Arbeitsabläufe im Bereich der aufsichtsrechtlichen Berichterstattung?
Bewährte Verfahren für eine reibungslose CRA-Implementierung
- Die Erstellung der SBOM frühzeitig integrieren („Shift Left“)
- Abhängigkeitszuordnung automatisieren
- SBOM-Daten von Lieferanten einholen
- Schulen Sie die Teams in Bezug auf ihre Aufgaben im Rahmen der CRA
Häufige Fehler, die es zu vermeiden gilt
| Fehler | Risiko | Milderung |
|---|---|---|
| SBOM als statisch behandeln | Bekannt gewordene Sicherheitslücke in veralteter Software | Kontinuierliche Aktualisierungen automatisieren |
| Transitive Abhängigkeiten ignorieren | Versteckte Risiken in der Lieferkette | Rekursives Abhängigkeits-Mapping verwenden |
| Manuelle SBOM-Prozesse | Inkonsistenz und fehlgeschlagene Prüfung | Automatisierte Werkzeuge implementieren |
Branchenspezifische Überlegungen
- Die Erstellung der SBOM frühzeitig integrieren („Shift Left“)
- Abhängigkeitszuordnung automatisieren
- SBOM-Daten von Lieferanten einholen
- Schulen Sie die Teams in Bezug auf ihre Aufgaben im Rahmen der CRA
Kritische und wichtige Produkte
Betriebssysteme, Hypervisoren, Firewalls und grundlegende Infrastrukturkomponenten stehen unter verstärkter Beobachtung.
Finanzdienstleistungen
Unternehmen müssen die Einhaltung der CRA-Vorschriften mit den übergeordneten EU-Rahmenwerken für Cybersicherheit (z. B. DORA) in Einklang bringen.
Industrial IoT
Bei eingebetteter Software müssen die Dokumentation langfristig aufbewahrt und Schwachstellen überwacht werden.
OPSWAT SBOM
OPSWAT bietet Teams folgende Vorteile:
- Genaue Bestandsaufnahmen von Softwarekomponenten
- Erstellung von SBOMs für Quellcode und Container
- Korrelation von Sicherheitslücken
- Transparenz bei der Lizenzierung
SBOM für Software und Artefakte
Open-Source-Risiken identifizieren, priorisieren und beheben, ohne die Entwicklung zu verlangsamen.
SBOM für Container
Erstellen Sie SBOMs auf jeder Containerebene und erkennen Sie Schwachstellen vor der Bereitstellung.
MetaDefender Software Supply Chain™
Gehen Sie über die reine Dokumentation hinaus und bekämpfen Sie komplexe Bedrohungen in der Lieferkette.
MetaDefender Software Chain™ integriert Zero-Trust-Prüfungen in den Softwareentwicklungszyklus (SDLC), indem es Multiscanning mit über 30 Antiviren-Engines, die Erkennung fest codierter Geheimnisse, eine tiefgehende Analyse der Containerebene, die Identifizierung von Schwachstellen sowie native Integrationen mit Repositorys und CI/CD-Pipelines kombiniert, um Malware, offengelegte Anmeldedaten und Risiken durch Abhängigkeiten zu verhindern und gleichzeitig die Einhaltung von Rahmenwerken wie dem EU-Cyber-Resilience-Act zu unterstützen.
FAQs
Wann findet das CRA Anwendung?
Die Meldepflichten treten im September 2026 in Kraft. Die vollständige Anwendung beginnt im Dezember 2027.
Müssen SBOMs öffentlich zugänglich sein?
Nein. Sie müssen den Behörden auf begründeten Antrag hin vorgelegt werden.
Zählen Open-Source-Komponenten dazu?
Ja. Für alle integrierten Komponenten haftet der Hersteller.
Welche Strafen drohen bei Nichteinhaltung?
Bis zu 15 Millionen Euro oder 2,5 % des weltweiten Jahresumsatzes.
Ist eine Automatisierung erforderlich?
Auch wenn dies nicht ausdrücklich vorgeschrieben ist, ist die Automatisierung unerlässlich, um die Anforderungen an die Lebenszyklusüberwachung zu erfüllen.
Wie geht es weiter? Vorbereitung auf Durchsetzungsmaßnahmen der CRA
Die CRA macht die Sicherheit der Software-Lieferkette zu einer Voraussetzung für die Geschäftstätigkeit auf dem EU-Markt und verlangt dabei Rechenschaftspflicht über den gesamten Lebenszyklus, eine kontinuierliche Überwachung von Sicherheitslücken sowie eine strukturierte SBOM-Dokumentation. Unternehmen, die bereits jetzt damit beginnen, ihre Entwicklungs- und Sicherheitsprozesse aufeinander abzustimmen, können ihr regulatorisches Risiko verringern und gleichzeitig ihre allgemeine Widerstandsfähigkeit stärken.
OPSWAT die Umsetzung der CRA-Anforderungen, indem es die Automatisierung von SBOMs, Informationen zu Sicherheitslücken, Multiscanning und Zero-Trust-Prüfungen direkt in die Entwicklungsabläufe integriert. So hilft das Unternehmen Herstellern dabei, ihre Software-Lieferketten zu stärken und gleichzeitig die Prüfungsbereitschaft aufrechtzuerhalten.
Erfahren Sie, wie OPSWAT Ihrem Unternehmen dabei helfen OPSWAT , die CRA-Anforderungen umzusetzen und die Sicherheit Ihrer Software-Lieferkette zu stärken.

