What is a Transfer Cross-Domain Solution?
A transfer cross-domain solution is a specialized security architecture that enables controlled data transfer between networks operating at different classification levels. In high-assurance environments, that control must be enforceable, auditable, and resistant to both external attacks and internal misuse.
Relying solely on a firewall introduces risk because software controls can fail, be misconfigured, or be exploited.
Cross-domain solutions exist because missions demand data sharing across security classifications. But every transfer is a potential attack path. In defense and critical infrastructure environments, that path cannot be left to software controls alone.
The Operational Risks of Cross-Domain Data Transfer
Cross-domain data transfer is now continuous, not occasional. Defense teams import patches, applications, and intelligence feeds from lower domains. Critical infrastructure operators move data between OT and IT networks for analytics and reporting. The business requirement is clear: data must move.
Adversaries exploit that necessity. They embed malware in legitimate file types and weaponize routine updates to cross from low to high security domains. On the other side, poorly controlled file exports risk leaking classified or regulated information.
The Core Risks Facing CDS Architects Today
- Malware hidden in approved file types crossing from low to high security domains
- Sensitive data leakage during high to low exports
- Increasing data volumes and complex file formats
- Accreditation pressure to prove policy enforcement and auditability
- AI-assisted threats evading signature-based detection
This is the tension. Enable mission collaboration while preserving strict separation between domains of different trust levels.
Why Traditional and Legacy Controls Fall Short
Traditional network defenses were not designed to meet high-assurance cross-domain security requirements.
Firewalls and standard gateways depend on configurable software logic. In classified and mission-critical environments, that flexibility can introduce risk. Misconfiguration or exploitation can unintentionally create a bidirectional path between domains that were meant to remain strictly separated.
Legacy CDS deployments built around rigid, appliance-only models often struggle to adapt. Data volumes continue to grow, file types are increasingly complex, and threat actors deliberately craft payloads designed to bypass superficial inspection.
Control Gaps in High-Assurance Cross-Domain Architectures
| Traditional or Software-Based Controls | High-Assurance CDS Requirement |
|---|---|
| Software-enforced bidirectional protocols | Hardware-enforced one-way transfer where required |
| Signature-based malware detection | Layered inspection, including multiscanning, CDR, and sandboxing |
| Basic file type filtering | Deep content inspection of embedded objects, macros, and metadata |
| Manual or loosely governed exports | Policy-driven release controls and audit trails |
| Static architecture | Modular design that scales with data types and mission needs |
Logical separation is not the same as physical separation. High-assurance cross-domain solutions require deterministic boundary enforcement combined with deep, policy-based inspection of every file or data stream before it is trusted to cross domains.
Data Diodes as the Foundation of Transfer CDS
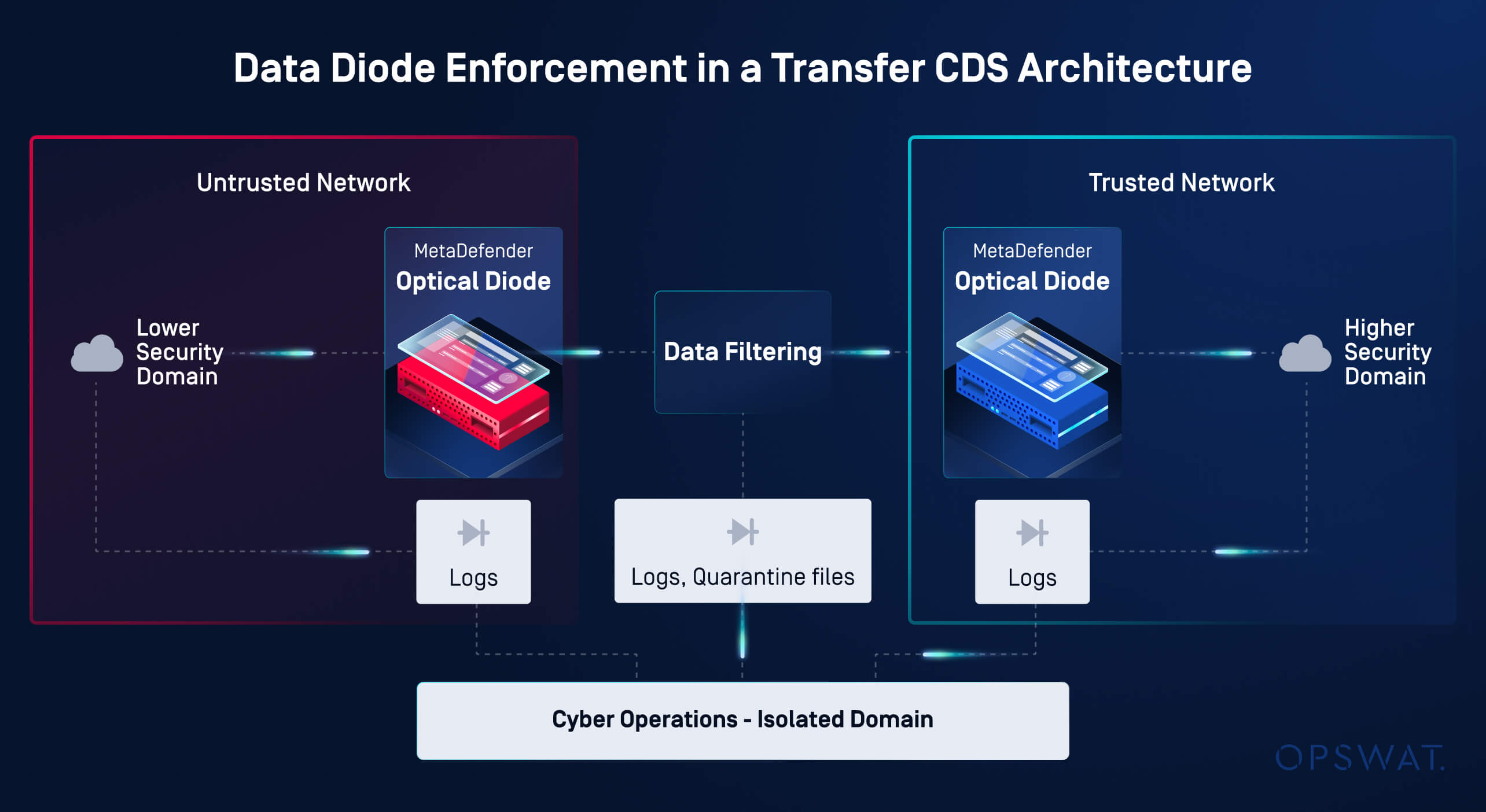
In a Transfer CDS, data must securely move between domains operating at different classification levels. To preserve separation while enabling that movement, data diodes enforce a physically one-way transfer at the boundary.
The diode sits between the security domains and the inspection layer. Its role is simple but critical. Data can move in only one direction. In high-assurance implementations, the diode prevents bidirectional communication by eliminating the return path at the network boundary. Only the intended data payload is allowed to cross domains.
A Typical Low-to-High Transfer Workflow
- A first diode moves data into a controlled inspection zone for deep content inspection
- Filtering and policy enforcement sanitize the content
- A second diode moves only approved data into the high security domain
The diode does not replace inspection. It enforces physical separation. Combined with layered inspection and policy validation, this is what transforms a data transfer mechanism into a high-assurance Transfer CDS architecture.
Building a Scalable, High-Assurance Transfer CDS Architecture
Building a scalable, high-assurance Transfer CDS architecture requires more than a hardware boundary. A Transfer CDS is a structured process that moves data through hardware-enforced separation, deep inspection, and strict policy validation before it ever reaches a higher security domain.
OPSWAT operationalizes this model through a modular architecture built on the MetaDefender™ Platform. Instead of relying on a single filtering step, SEFs are layered and tuned according to transfer direction, data type, and mission risk.
Low-to-High Transfers: Preventing Malware Ingress
Metascan™ Multiscanning with 30+ antimalware engines to reduce reliance on a single detection source
Deep CDR™ Technology to disassemble and reconstruct files using only verified, safe elements
Metadata removal to strip hidden information such as embedded authorship data or revision history
Adaptive Sandbox™ to detect evasive or zero-day behavior
Vulnerability Assessment to identify known weaknesses within transferred files
High-to-Low Transfers: Preventing Data Leakage
Proactive DLP™ to detect and block unauthorized classified or regulated information
Policy-driven validation that strictly defines which file types and content elements may cross
Detailed audit trails to support accreditation and compliance reviews
All of this operates in conjunction with MetaDefender Optical Diode™ and MetaDefender NetWall™ gateways, which provide hardware-enforced one-way transfer and protocol separation between domains. The diode guarantees direction. The SEFs determine what is permitted to cross.
The result is a scalable Transfer CDS architecture aligned with defense, intelligence, and critical infrastructure requirements. It supports system and software imports, controlled exports, removable media workflows, and multi-domain collaboration without weakening domain separation or accreditation posture.
Enabling Secure Collaboration Without Compromising Separation
Cross-domain solutions exist because missions require controlled data sharing across trust boundaries. The risk is not in moving data. The risk is in moving it without deterministic enforcement and deep validation.
Traditional controls rely on logical rules. High-assurance CDS architectures combine hardware-enforced one-way transfer with layered inspection, policy enforcement, and auditability. This transforms a network connection into a controlled boundary.
By integrating layered SEFs with MetaDefender Optical Diode and MetaDefender NetWall gateways, OPSWAT Cross-Domain Solutions deliver secure data transfer aligned with defense, intelligence, and critical infrastructure requirements.
Practical and Measurable Outcomes
- Malware is prevented from entering high-security domains during low to high imports
- Sensitive or classified data is blocked from leaking during high-to-low exports
- Every transfer is governed by policy and backed by audit evidence
- Mission collaboration continues without weakening domain separation
We cannot eliminate the need to share data across domains. But we can control how it moves, how it is inspected, and how it is enforced.
If you are designing or modernizing a high-assurance cross-domain architecture, evaluate whether your boundary is logically configured or physically enforced. Contact an OPSWAT expert to explore a modular, scalable Transfer CDS approach.
FAQs
What is a Transfer Cross-Domain Solution (CDS)?
A Transfer Cross-Domain Solution (CDS) is a high-assurance security architecture that enables controlled data transfer between networks operating at different classification levels. A Transfer CDS combines hardware-enforced separation—such as one-way data diodes—with layered Security Enforcing Functions (SEFs), including multiscanning, Content Disarm and Reconstruction (CDR), sandboxing, and Data Loss Prevention (DLP). This model prevents malware ingress and sensitive data leakage while preserving deterministic separation between domains.
Why are data diodes required in high-assurance CDS architectures?
Data diodes enforce physically one-way data flows at the hardware level, eliminating the return path between domains. In high-assurance environments, logical controls such as firewalls are insufficient because they rely on configurable software rules. A data diode provides deterministic boundary enforcement, ensuring that communication remains unidirectional and compliant with cross-domain accreditation requirements.
How does a Transfer CDS prevent malware from crossing domains?
A Transfer CDS prevents malware ingress through layered inspection using Security Enforcing Functions (SEFs). These may include Metascan™ Multiscanning with multiple antimalware engines, Deep CDR™ Technology to rebuild files using verified elements, Adaptive Sandbox™ analysis for zero-day detection, and vulnerability assessment. Combined with hardware-enforced one-way transfer, these controls ensure that only sanitized, policy-approved data is allowed to cross domains.
How does a Transfer CDS prevent sensitive data leakage?
For high-to-low transfers, a Transfer CDS applies strict policy validation and Data Loss Prevention (DLP) controls before any data leaves a secure domain. Capabilities such as Proactive DLP™, metadata removal, file-type enforcement, and detailed audit logging ensure that classified or regulated information cannot be exported without authorization. This layered approach supports accreditation and compliance requirements.
What makes OPSWAT’s approach to Transfer CDS different?
OPSWAT’s Transfer CDS architecture combines MetaDefender Optical Diode™ hardware with layered Security Enforcing Functions built on the MetaDefender™ Platform. Capabilities such as Metascan™ Multiscanning, Deep CDR™ Technology, Adaptive Sandbox™, Proactive DLP™, and policy-driven validation operate together to enforce direction and determine what content is permitted to cross. This modular design supports defense, intelligence, and critical infrastructure environments requiring high-assurance separation.
Can a firewall replace a data diode in a cross-domain solution?
No. A firewall enforces configurable software rules and typically supports bidirectional communication. A data diode enforces physical one-way data flow at the hardware layer, eliminating the return path between domains. In high-assurance Transfer CDS environments, hardware-enforced separation is required to achieve deterministic boundary protection and meet accreditation expectations.

