
Bewährte Verfahren für die Sicherheit des Netzwerkverkehrs im Jahr 2026
Secure Netzwerkverkehr vor dateibasierter Malware, Zero-Day-Bedrohungen und Datenlecks. Dieses Whitepaper beschreibt wichtige Sicherheitsmaßnahmen, eine zentralisierte ICAP Überprüfung, eine Checkliste zur Sicherheitsbereitschaft sowie ein strukturiertes Reifegradmodell, um Unternehmen dabei zu unterstützen, ihre Zero-Trust-Resilienz zu stärken.
Unternehmensrisiken über alle Datenströme hinweg reduzieren
Erfahren Sie, wie mehrschichtige Überwachung und interne Transparenz das Risiko von Ransomware-Angriffen verringern, die laterale Bewegung einschränken und regulierte Daten vor Zero-Day-Angriffen und DDoS-basierten Kompromittierungen schützen.

Sichern Sie sich optimalen Schutz durch mehrschichtige Sicherheitsmaßnahmen
Nutzen Sie mehrere Anti-Malware-Engines, Sandboxing und Verhaltensanalysen, um Erkennungsraten von über 99 % zu erzielen und Zero-Day-Bedrohungen abzuwehren. Reduzieren Sie Sicherheitslücken, ohne die Leistung zu beeinträchtigen, und setzen Sie gleichzeitig einheitliche Richtlinien für den gesamten Datenverkehr durch.
Erhalten Sie einen klaren Fahrplan für die Umsetzung von Zero Trust
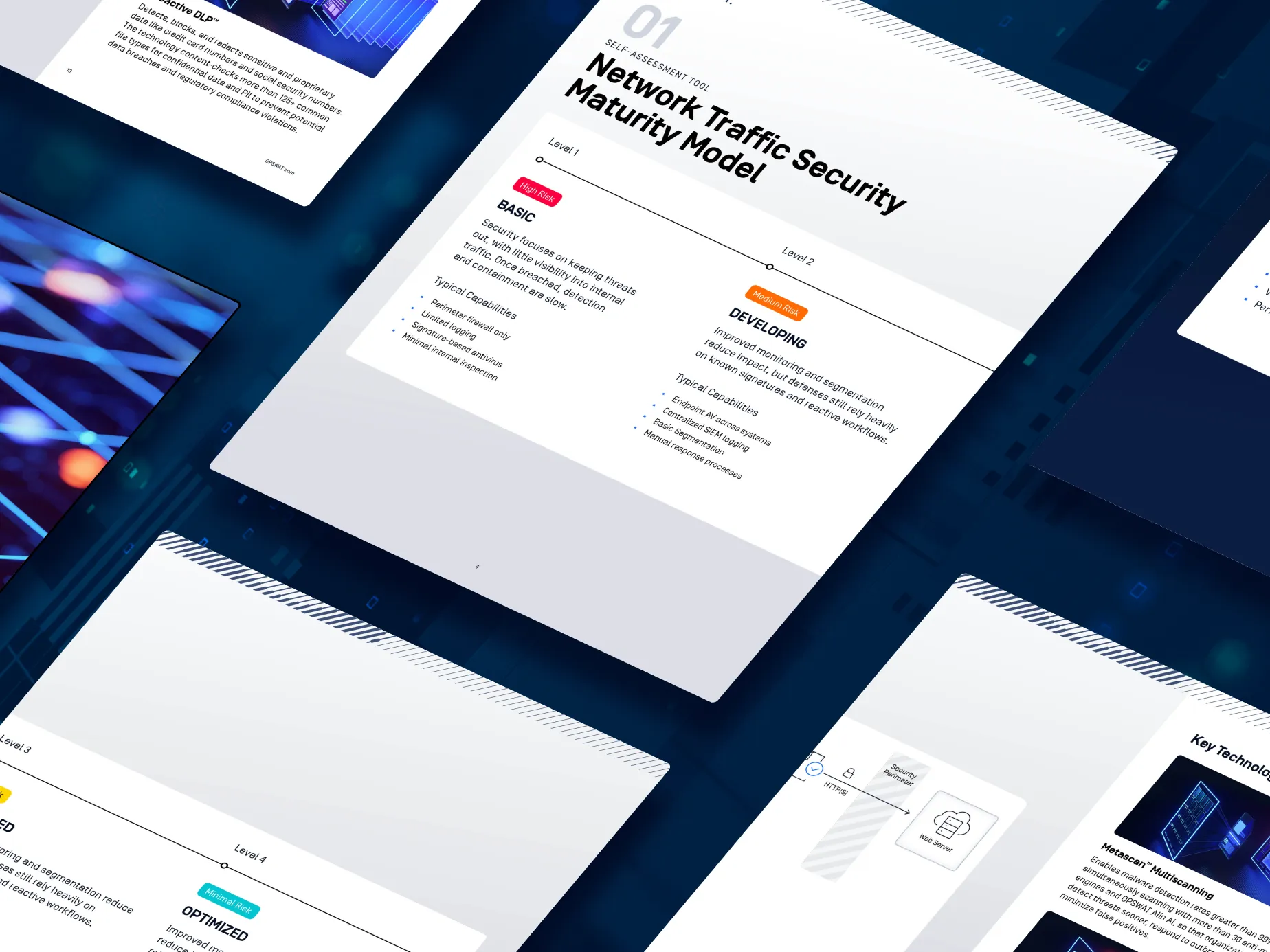
Holen Sie sich eine Checkliste zur Sicherheitsbereitschaft, um Schwachstellen zu identifizieren, Investitionen zu priorisieren und die messbare Risikominderung zu beschleunigen, sowie ein praktisches Reifegradmodell für die Sicherheit des Netzwerkverkehrs, um Ihren aktuellen Stand zu bewerten.

Stärken Sie Ihre Strategie zur Sicherung des Netzwerkverkehrs
Laden Sie das Whitepaper herunter, um Ihren Reifegrad zu ermitteln, die Erkennungsrate auf über 99 % zu steigern und Zero Trust mithilfe zentralisierter Überwachung und automatisierter Abwehrmaßnahmen umzusetzen.
